Here at ZKX Solutions, prospective customers or business partners often ask us how we go about structuring a good defensive cybersecurity posture. Our philosophy at ZKX covers three primary abstract categories that fully encompass what a good defensive cybersecurity posture looks like.
- Policy: This is the written set of rules, or organizational guidelines, that instruct users on how to use technologies. This includes your end users that consume these technological products and services and your administrators that set up and configure them.
- Technology: The tools and devices your organization has at its disposal for your users to accomplish their objectives.
- Culture: How users interact with each other and with these technologies.
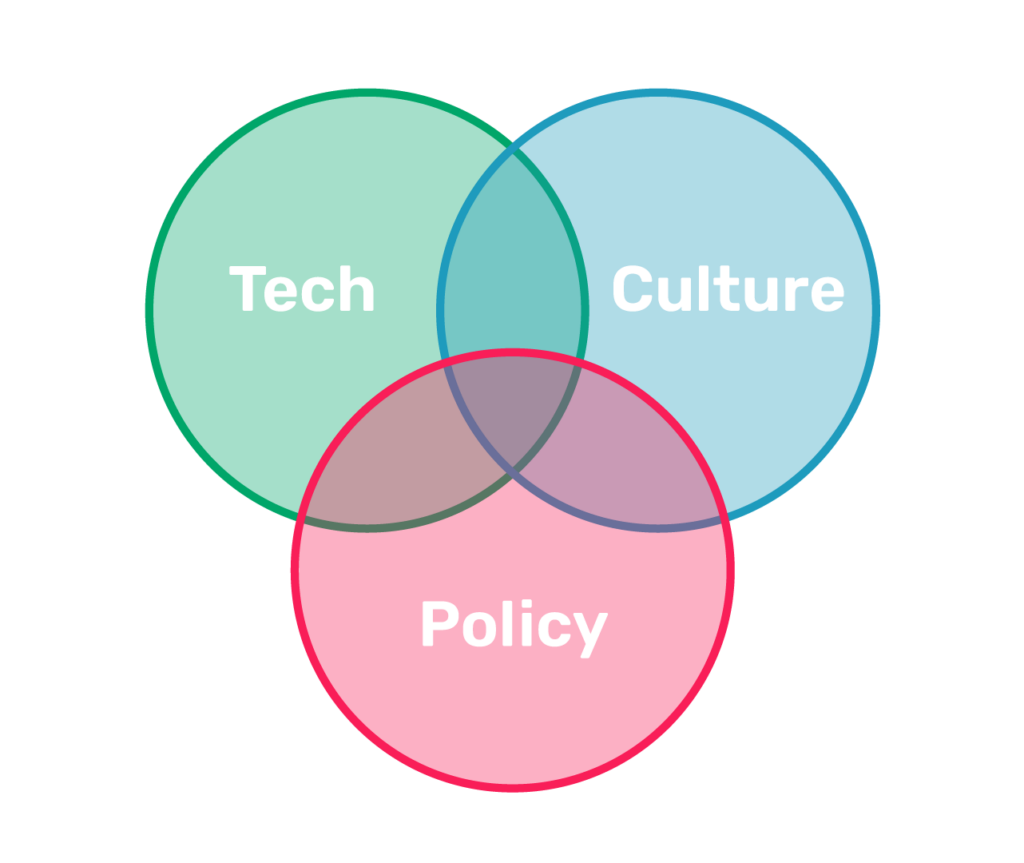
It’s important to note that these three categories don’t exist in isolation. In fact, there’s a distinct overlap where technology, policy, and culture all intersect. This can be exemplified through a couple of different examples. If your organization has fallen into the unfortunate trap of chasing the “latest and greatest” technologies, the organizational guidelines for configuring and utilizing this new technology may not be sufficient. If it doesn’t meet your organizational security profile, or you’re comfortable with accepting the level of risk that comes with this new novel solution, this may result in insufficient policies surrounding the use of this new technology. This, in turn, can create a weakness that a malicious actor can exploit and use to breach your systems.
Similarly, if you have a body of policy that sufficiently governs how your users should use or employ these different technologies, but the technologies that you have at your organization’s disposal do not sufficiently meet your current pace of day-to-day operations, adversaries can target these weak or outdated technologies in order to exploit your overall security posture, and wreak havoc on your system internally.
The last and arguably most important category is culture. A good operating culture is often the first line of defense against common social engineering attacks, such as phishing or spearfishing. Good culture is cultivated by good technology or good policy; if one of those distinct categories is lacking, it can create a weakness in your cybersecurity foundation. For example, if you have a sufficient technological profile and a decent body of policy governing how those technologies should be used, or if you have a poor operating culture amongst your end users – say, an unwillingness to report phishing emails – this too can leave your cybersecurity posture vulnerable to adversaries.
At ZKX Solutions, we firmly believe that the intersection between technology, policy, and culture is critical for maintaining a sufficient defensive cybersecurity posture. At ZKX, the technologies and information resources we develop daily are built to service your journey to a mature, defensive cybersecurity posture by focusing on policy, technology, and culture.