
Identity and Access Management (IAM): Where ZKX Helix Fits In
A man-in-the-middle attack involves a malicious actor intercepting packets sent from a user to a secure application. Here is how ZKX Helix can help prevent them.
Filter by Category:

A man-in-the-middle attack involves a malicious actor intercepting packets sent from a user to a secure application. Here is how ZKX Helix can help prevent them.
A man-in-the-middle attack involves a malicious actor intercepting packets sent from a user to a secure application. Here is how ZKX Helix can help prevent them.
Understanding their difference between authentication and authorization is very important when implementing security in a system. Here we explain the differences you need to know.

Multi-factor authentication (MFA) is one of the most effective ways to secure systems against unauthorized access. Our authentication platform is specifically designed to handle both IT and OT environments, delivering flexible, precise, and secure multi-factor authentication tailored to the unique priorities and constraints of each environment.
The Salt Typhoon cyber attacks have been some of the most consequential this century. ZKX Helix is designed to strengthen exactly the kinds of access controls that Salt Typhoon breached; here’s how.

ZKX Solutions, a pioneer in developing the next generation of cyber defense technology, has officially released its new product, ZKX Helix. ZKX Helix enables holistic IT, OT, and IoT cybersecurity by safeguarding multiple network and resource access layers with pinpoint accuracy.
ZKX Solutions recently completed technical exercises at C5ISR’s NetModX event at Ft. Dix, New Jersey. ZKX Helix, was used to bring zero-trust access control into the U.S. Army’s command and control capabilities through REDCOM’s Sigma platform.
ZKX Solutions has recently completed a successful product demonstration at the U.S. Army Cyber Quest 24 event at Fort Eisenhower in Augusta, GA. The Cyber Quest Demonstration included Helix coupled with the Viasat Variable Trust Stack, ZKX enables dynamic and conditional access to sensitive resources based on real-time data such as geolocation.

AT&T has confirmed a data breach of call and text records between May 1, 2022, and October 31, 2022. In this article, we explain how Helix’s patented MFA system would have prevented the data breach and kept customers safe. By utilizing Zero Knowledge Proofs and Zero Trust Policies, bad actors cannot phish login information or crack passwords through traditional methods.
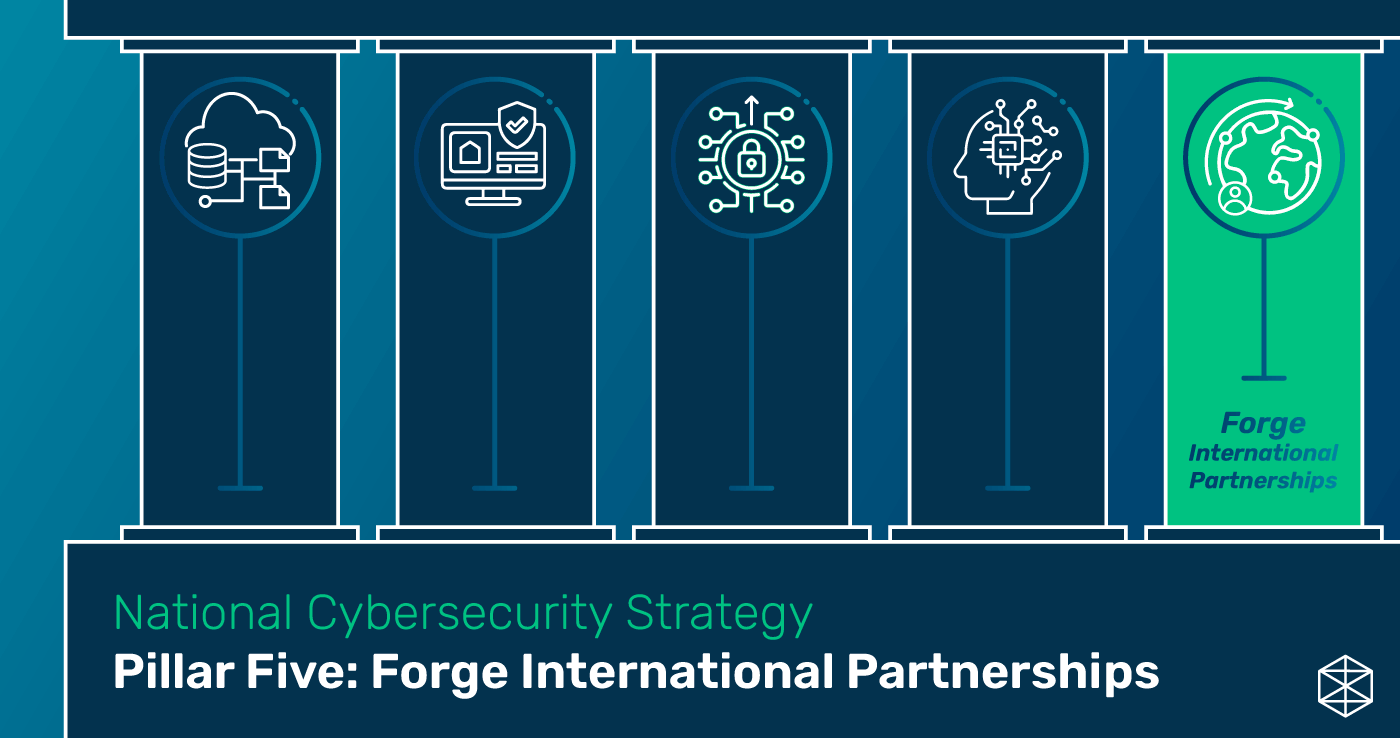
Creating a strong and united international community is the key to fostering a shared digital ecosystem that is inherently resilient and defensible. The United States is committed to working with a coalition of cyber security stakeholders within the international community to disrupt transnational cyber criminals and reinforce international law in cyberspace.

Investments in technology and culture need to be made today to ensure a resilient future. By combining federal and private sector resources, we can leverage investments in R&D, innovation, and education to enhance our digital presence and cyber infrastructure. However, innovation is not enough. Without making cybersecurity a top priority, our innovation and technological advancements are open for infiltration by our adversaries.

ZKX Solutions, a pioneer in developing the next generation of cyber defense technology, today announced that the U.S. Patent and Trademark Office has issued a new patent, no. 11,700,125, for an innovative new Multi-Factor Authentication (MFA) system.